Internet of things – Typical attacks and countermeasures
ABSTRACT
Internet security has been the subject of much debate over the past decade. Nowadays
every industry and every business sector is aware of the importance of cybersecurity,
however, the effects of the 4.0 revolution have raised issues of security and secure Internet
connection. At the present time, the world is at the beginning of the fourth industrial
revolution, one of its most prominent applications, the Internet of Things, which has shown a
strong impact on all areas and the edge of life. The core of Internet of Things is the idea of
using cyberspace as a means to improve performance, productivity, and customization of
things. Through this, data is collected and transmitted from various things, such as production
line equipment, sensors in the product at the customer base, sales data and more. This intense
and continuous impact of Internet of Things has expanded the complexity of data security and
information as things connect in the future.
In an effort to shed light on the development of security on the Internet when the trend
of typical application of the 4.0 Industrial Revolution is the Internet of Things developing
robust, this article tries to identify risks in a connected business. The main purpose of this
article is to show that the emergence of Internet of Things will reduce the gap between
existing security and security. Based on that, the paper proposes some practical solutions to
ensure Internet security for data transmission when things are connected.
Trang 1
Trang 2
Trang 3
Trang 4
Trang 5
Trang 6
Trang 7
Trang 8
Trang 9
Tóm tắt nội dung tài liệu: Internet of things – Typical attacks and countermeasures

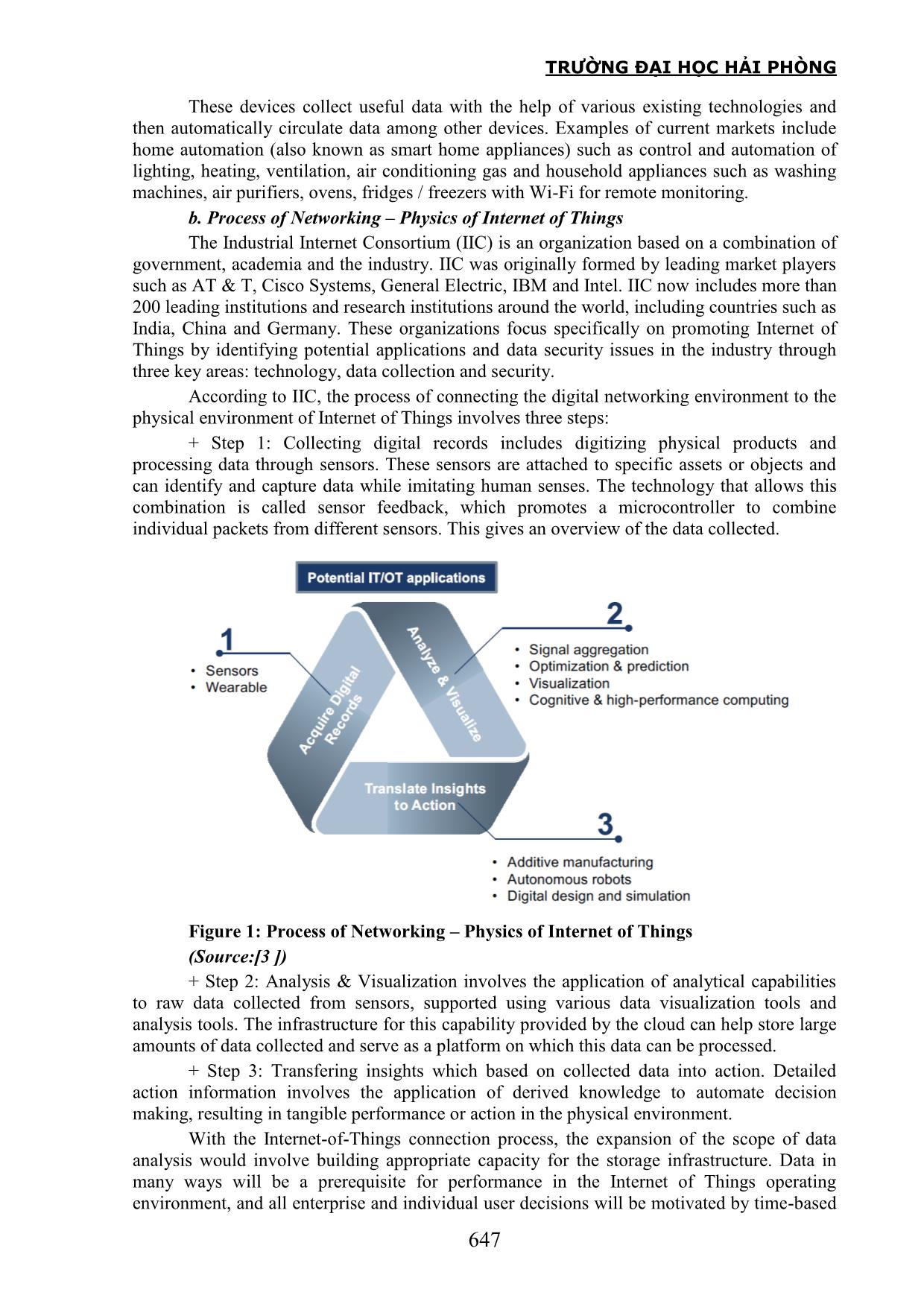
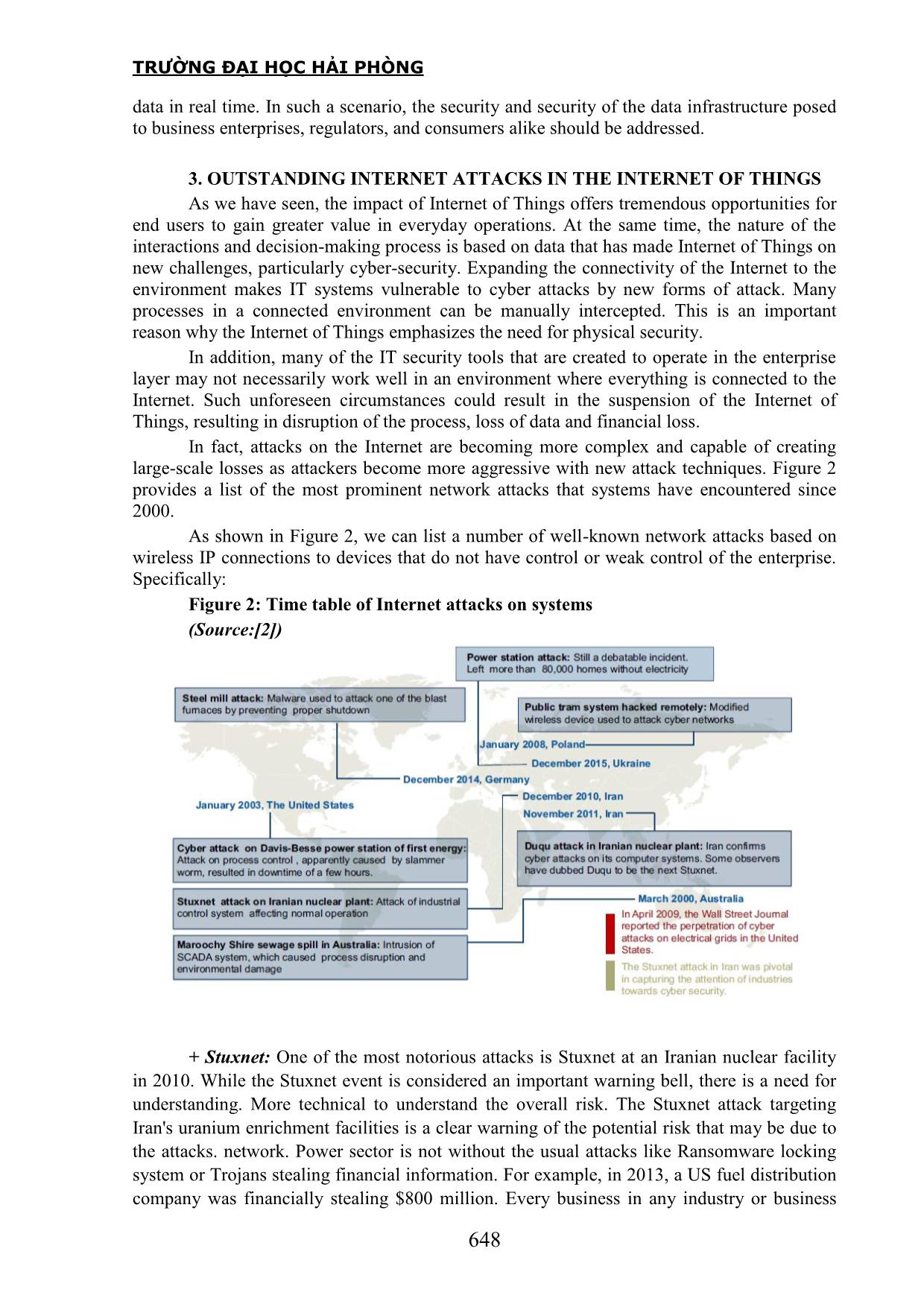
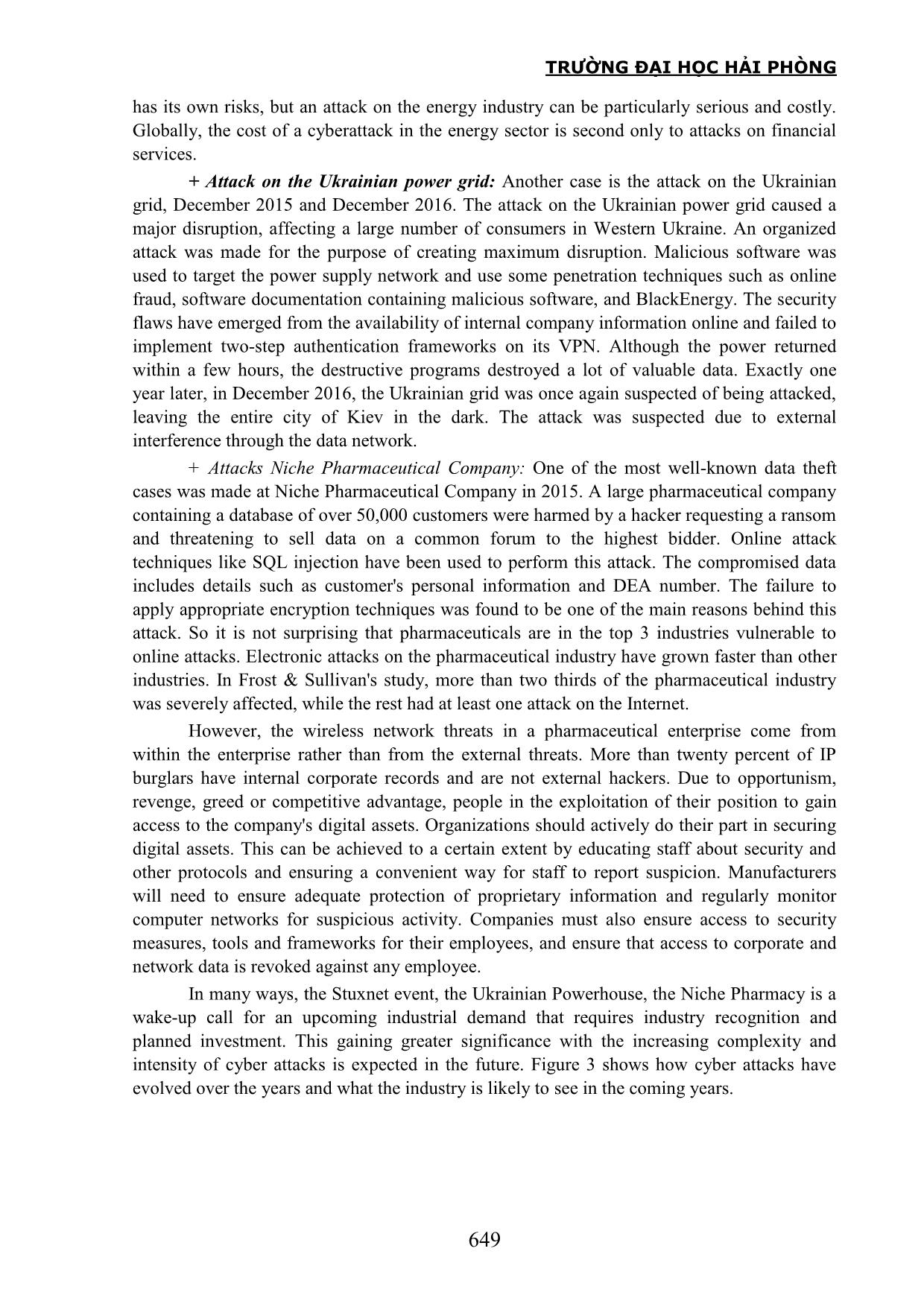
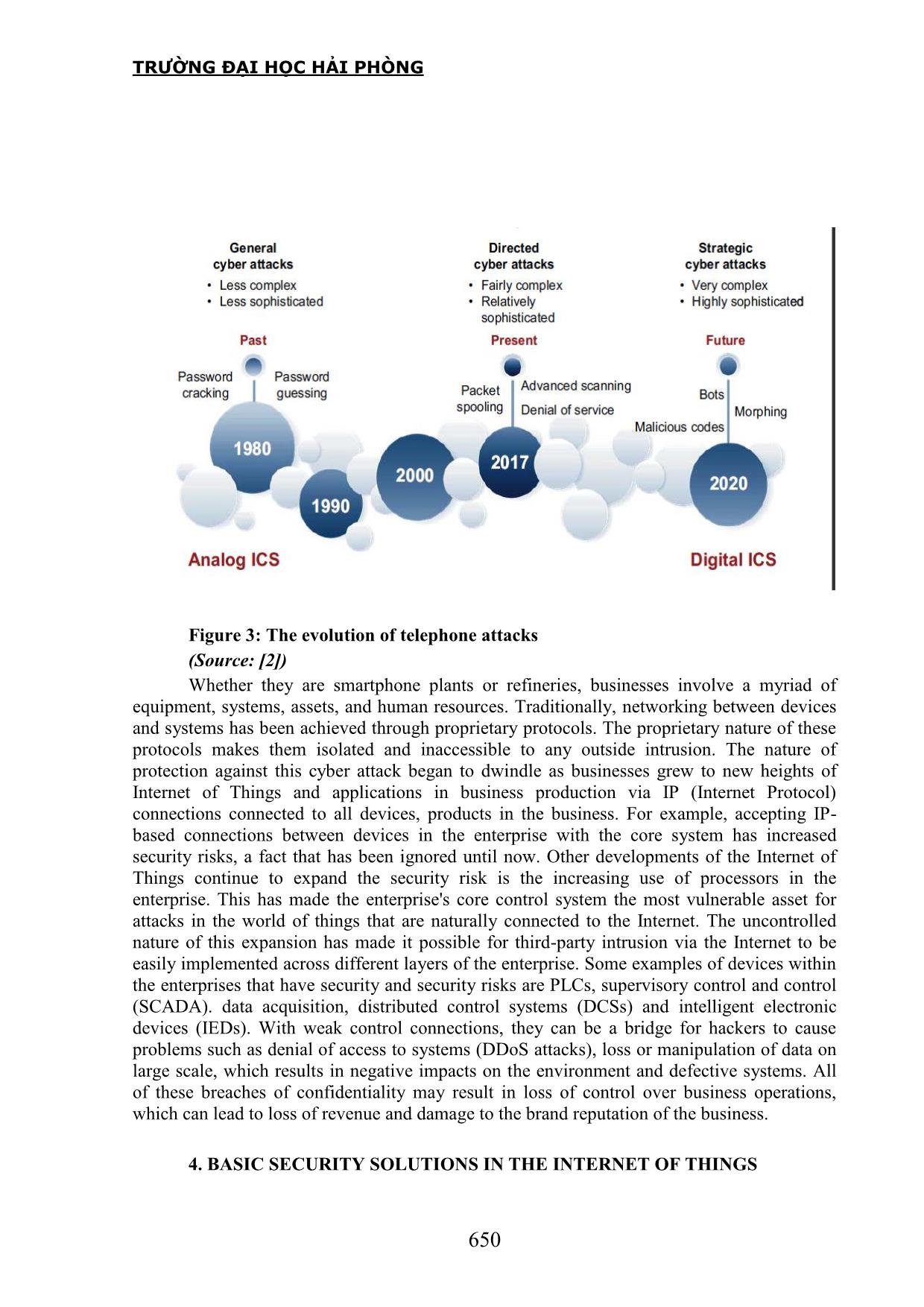
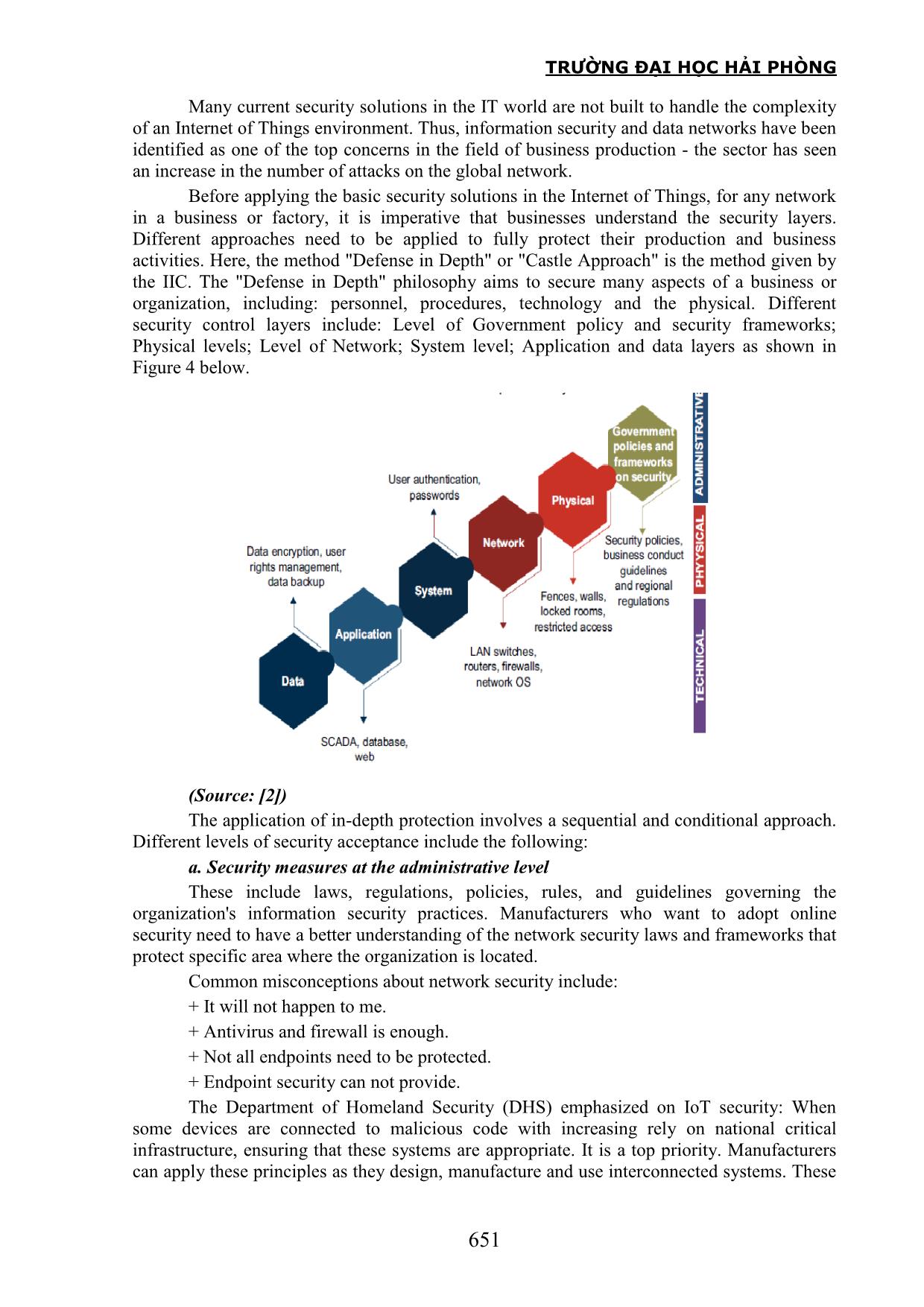
ing is connected to the Internet. Such unforeseen circumstances could result in the suspension of the Internet of Things, resulting in disruption of the process, loss of data and financial loss. In fact, attacks on the Internet are becoming more complex and capable of creating large-scale losses as attackers become more aggressive with new attack techniques. Figure 2 provides a list of the most prominent network attacks that systems have encountered since 2000. As shown in Figure 2, we can list a number of well-known network attacks based on wireless IP connections to devices that do not have control or weak control of the enterprise. Specifically: Figure 2: Time table of Internet attacks on systems (Source:[2]) + Stuxnet: One of the most notorious attacks is Stuxnet at an Iranian nuclear facility in 2010. While the Stuxnet event is considered an important warning bell, there is a need for understanding. More technical to understand the overall risk. The Stuxnet attack targeting Iran's uranium enrichment facilities is a clear warning of the potential risk that may be due to the attacks. network. Power sector is not without the usual attacks like Ransomware locking system or Trojans stealing financial information. For example, in 2013, a US fuel distribution company was financially stealing $800 million. Every business in any industry or business TRƯỜNG ĐẠI HỌC HẢI PHÒNG 649 has its own risks, but an attack on the energy industry can be particularly serious and costly. Globally, the cost of a cyberattack in the energy sector is second only to attacks on financial services. + Attack on the Ukrainian power grid: Another case is the attack on the Ukrainian grid, December 2015 and December 2016. The attack on the Ukrainian power grid caused a major disruption, affecting a large number of consumers in Western Ukraine. An organized attack was made for the purpose of creating maximum disruption. Malicious software was used to target the power supply network and use some penetration techniques such as online fraud, software documentation containing malicious software, and BlackEnergy. The security flaws have emerged from the availability of internal company information online and failed to implement two-step authentication frameworks on its VPN. Although the power returned within a few hours, the destructive programs destroyed a lot of valuable data. Exactly one year later, in December 2016, the Ukrainian grid was once again suspected of being attacked, leaving the entire city of Kiev in the dark. The attack was suspected due to external interference through the data network. + Attacks Niche Pharmaceutical Company: One of the most well-known data theft cases was made at Niche Pharmaceutical Company in 2015. A large pharmaceutical company containing a database of over 50,000 customers were harmed by a hacker requesting a ransom and threatening to sell data on a common forum to the highest bidder. Online attack techniques like SQL injection have been used to perform this attack. The compromised data includes details such as customer's personal information and DEA number. The failure to apply appropriate encryption techniques was found to be one of the main reasons behind this attack. So it is not surprising that pharmaceuticals are in the top 3 industries vulnerable to online attacks. Electronic attacks on the pharmaceutical industry have grown faster than other industries. In Frost & Sullivan's study, more than two thirds of the pharmaceutical industry was severely affected, while the rest had at least one attack on the Internet. However, the wireless network threats in a pharmaceutical enterprise come from within the enterprise rather than from the external threats. More than twenty percent of IP burglars have internal corporate records and are not external hackers. Due to opportunism, revenge, greed or competitive advantage, people in the exploitation of their position to gain access to the company's digital assets. Organizations should actively do their part in securing digital assets. This can be achieved to a certain extent by educating staff about security and other protocols and ensuring a convenient way for staff to report suspicion. Manufacturers will need to ensure adequate protection of proprietary information and regularly monitor computer networks for suspicious activity. Companies must also ensure access to security measures, tools and frameworks for their employees, and ensure that access to corporate and network data is revoked against any employee. In many ways, the Stuxnet event, the Ukrainian Powerhouse, the Niche Pharmacy is a wake-up call for an upcoming industrial demand that requires industry recognition and planned investment. This gaining greater significance with the increasing complexity and intensity of cyber attacks is expected in the future. Figure 3 shows how cyber attacks have evolved over the years and what the industry is likely to see in the coming years. TRƯỜNG ĐẠI HỌC HẢI PHÒNG 650 Figure 3: The evolution of telephone attacks (Source: [2]) Whether they are smartphone plants or refineries, businesses involve a myriad of equipment, systems, assets, and human resources. Traditionally, networking between devices and systems has been achieved through proprietary protocols. The proprietary nature of these protocols makes them isolated and inaccessible to any outside intrusion. The nature of protection against this cyber attack began to dwindle as businesses grew to new heights of Internet of Things and applications in business production via IP (Internet Protocol) connections connected to all devices, products in the business. For example, accepting IP- based connections between devices in the enterprise with the core system has increased security risks, a fact that has been ignored until now. Other developments of the Internet of Things continue to expand the security risk is the increasing use of processors in the enterprise. This has made the enterprise's core control system the most vulnerable asset for attacks in the world of things that are naturally connected to the Internet. The uncontrolled nature of this expansion has made it possible for third-party intrusion via the Internet to be easily implemented across different layers of the enterprise. Some examples of devices within the enterprises that have security and security risks are PLCs, supervisory control and control (SCADA). data acquisition, distributed control systems (DCSs) and intelligent electronic devices (IEDs). With weak control connections, they can be a bridge for hackers to cause problems such as denial of access to systems (DDoS attacks), loss or manipulation of data on large scale, which results in negative impacts on the environment and defective systems. All of these breaches of confidentiality may result in loss of control over business operations, which can lead to loss of revenue and damage to the brand reputation of the business. 4. BASIC SECURITY SOLUTIONS IN THE INTERNET OF THINGS TRƯỜNG ĐẠI HỌC HẢI PHÒNG 651 Many current security solutions in the IT world are not built to handle the complexity of an Internet of Things environment. Thus, information security and data networks have been identified as one of the top concerns in the field of business production - the sector has seen an increase in the number of attacks on the global network. Before applying the basic security solutions in the Internet of Things, for any network in a business or factory, it is imperative that businesses understand the security layers. Different approaches need to be applied to fully protect their production and business activities. Here, the method "Defense in Depth" or "Castle Approach" is the method given by the IIC. The "Defense in Depth" philosophy aims to secure many aspects of a business or organization, including: personnel, procedures, technology and the physical. Different security control layers include: Level of Government policy and security frameworks; Physical levels; Level of Network; System level; Application and data layers as shown in Figure 4 below. Figure 4: Enterprise security layers in IoT (Source: [2]) The application of in-depth protection involves a sequential and conditional approach. Different levels of security acceptance include the following: a. Security measures at the administrative level These include laws, regulations, policies, rules, and guidelines governing the organization's information security practices. Manufacturers who want to adopt online security need to have a better understanding of the network security laws and frameworks that protect specific area where the organization is located. Common misconceptions about network security include: + It will not happen to me. + Antivirus and firewall is enough. + Not all endpoints need to be protected. + Endpoint security can not provide. The Department of Homeland Security (DHS) emphasized on IoT security: When some devices are connected to malicious code with increasing rely on national critical infrastructure, ensuring that these systems are appropriate. It is a top priority. Manufacturers can apply these principles as they design, manufacture and use interconnected systems. These TRƯỜNG ĐẠI HỌC HẢI PHÒNG 652 guidelines are important to help businesses make security decisions. The main high-level principles defined by DHS include: + Combining security at the design stage: With the intention to maximize profits in a shorter time, manufacturers fail to secure their systems and processes. This leaves room for hackers to manipulate information in the network. The guidelines are set by DHS but instruct manufacturers to incorporate these principles into network security right from the design stage. + Activation of security updates and vulnerability management: The old industrial machines are vulnerable to attack. These vulnerabilities can be solved by fixing vulnerabilities, providing security updates, and managing vulnerabilities. + Using the best proven security practices: Proven and proven security best practices can be a starting point for implementing effective security measures in Internet of Things. + Prioritized security by impact: The risks arising from network threats and corresponding access measures vary with the types of objects that are connected to the Internet. These security measures should be prioritized based on the magnitude and nature of potential impact. + Enhancing transparency: Increasing transparency and visibility in plant processes can help determine where and how to implement security measures. + Careful consideration of connectivity: Industrial enterprises should thoroughly analyze their business practices and understand whether there is a need for continuous connectivity when considering the risks associated with connectivity. b. Security solutions at the grassroots level (physical) Safeguards at the grassroots level can help companies build and maintain a positive reputation with their customers. Improving enterprise security also means improving productivity because it helps prevent unwanted theft or loss of data. This in turn can help expand business opportunities. At all times, businesses must ensure that the material aspects of the facilities include identifying and monitoring individuals in and out of the business. Businesses also need to track the movement of assets, equipment in the enterprise and supply chain, controlling access to sensitive areas in the enterprise. They also need to be constantly alerted by optimizing response times with potential threats and alerts. c. Security measures at the technical level This includes the technological components of a network security system that helps protect connected assets. Many IT security providers provide end-to-end protection solutions, but not all provide comprehensive security for endpoints and the Internet of Things. For end users, any attack on the Internet of Things network can cause business losses and a loss of credibility. The growing complexity and intensity of wireless network attacks are driving demand not only to prevent a possible attack, but also to anticipate and prepare for future scenarios. It can happen if a real attack takes place. 5. CONCLUSION Industrial Revolution 4.0 brings many new technology trends, such as the Internet of Things, requiring a more rigorous approach to information security issues and attacks from wireless connection environment through objects or devices. The connection between devices, assets, processes, and people has made the boundaries between the internal and external network lighter and more favorable for attackers to attack the system - the core of a business or an organization. Ensuring Internet security in an increasingly complex environment has become an inevitable strategic need for end users in all sectors and business areas. In order to establish solutions in a holistic way, the all-power approach has been presented in a secure order that ensures the security of the layers with different aspects that the enterprise needs to TRƯỜNG ĐẠI HỌC HẢI PHÒNG 653 establish in operating environment to minimize the disadvantages and maximize the advantages of the trend of Internet connection. REFERENCE [1]. K. Ashton (2009), “That „Internet of Things‟ thing”, Retrieved 9 May 2017. [2]. Frost & Sullivan (2017), Cyber Security in the era of Industrial IOT, A Frost & Sullivan White Paper. [3]. HBR (2014), "Internet of Things: Science Fiction or Business Fact?" (PDF). Harvard Business Review. November 2014 Retrieved 23 October 2016. [4]. ITU (2015), Internet of Things Global Standards Initiative, ITU Retrieved 26 June 2015. [5]. T. Lindner(13July2015), "The Supply Chain: Changing at the Speed of Technology", Connected World, Retrieved 18 September 2015. [6]. F. Mattern & C. Floerkemeier (2016), "From the Internet of Computers to the Internet of Things" (PDF), ETH Zurich, Retrieved 23 October 2016. [7]. A. Nordrum (18 August 2016). Popular Internet of Things Forecast of 50 Billion Devices by 2020 Is Outdated, IEEE Spectrum. [8]. G. Santucci (2016), "The Internet of Things: Between the Revolution of the Internet and the Metamorphosis of Objects" (PDF). European Commission Community Research and Development Information Service, Retrieved 23 October 2016. [9]. O. Vermesan & P. Friess (2013), “Internet of Things: Converging Technologies for Smart Environments and Integrated Ecosystems” (PDF). Aalborg, Denmark: River Publishers. ISBN 978-87-92982-96-4. [10]. I. Wigmore (June 2014). "Internet of Things (IoT)", TechTarget, June 2014. [11].
File đính kèm:
 internet_of_things_typical_attacks_and_countermeasures.pdf
internet_of_things_typical_attacks_and_countermeasures.pdf